111.150.90.2004
The term 111.150.90.2004 looks unusual at first glance. It resembles an internet address, but its structure doesn’t match the exact format most people expect when they think about IP addresses or network identifiers. Because of this, many people who encounter it—whether in server logs, configuration files, or search results—often wonder what it actually represents and whether it has any technical significance.
In the world of networking, numbers formatted with dots usually indicate some type of address, identifier, or system reference. However, not every number that follows this style is necessarily a valid internet protocol address. Sometimes such sequences appear as placeholders, internal identifiers, database references, or even misformatted entries in network logs.
This article explores the possible meaning of 111.150.90.2004, how similar number sequences are used in networking environments, and what you should consider if you encounter it in real-world systems. The goal is to break down the topic in a practical and easy-to-understand way while still providing insights that someone with technical curiosity—or professional interest—can appreciate.
The Structure Behind 111.150.90.2004
When people first see 111.150.90.2004, they usually assume it is an IP address. Traditional IPv4 addresses follow a format of four numbers separated by dots, with each number ranging between 0 and 255. For example, a typical IPv4 address might look something like 192.168.1.1.
The sequence 111.150.90.2004 contains four dots but includes a number that exceeds the maximum allowed value for IPv4. Specifically, the segment 2004 goes beyond the 0–255 range, which means it cannot be interpreted as a standard IPv4 address. This immediately tells us that the number is likely something else—either a formatting error, a custom identifier, or a different type of numerical label.
In many technical systems, numbers formatted with dots are used purely for readability. Developers often use dot-separated identifiers to represent hierarchical data. For instance, a system might use a format like region.server.cluster.node or year.month.day.record. In such cases, 111.150.90.2004 may simply be a structured label that conveys internal information rather than a direct network address.
Possible Technical Meanings of 111.150.90.2004

Although 111.150.90.2004 is not a valid IPv4 address, it may still appear in several technical contexts. One possibility is that it represents a database reference or version identifier. Software systems frequently use dotted numbers to mark version levels, build identifiers, or patch sequences.
Another possibility is that the number sequence is part of a logging or monitoring system. When servers generate logs, they often record events using structured numeric codes. These codes can include timestamps, event categories, or server identifiers combined into a single formatted string. In that context, 111.150.90.2004 could be an internal tracking reference used by a specific platform or application.
It is also possible that the sequence is a malformed IP address that resulted from a data entry error or an automated script issue. Network logs sometimes contain corrupted entries when parsing scripts fail to process data correctly. When this happens, numbers that were meant to represent ports, timestamps, or identifiers may accidentally merge into a format that resembles an IP address.
Where You Might Encounter 111.150.90.2004
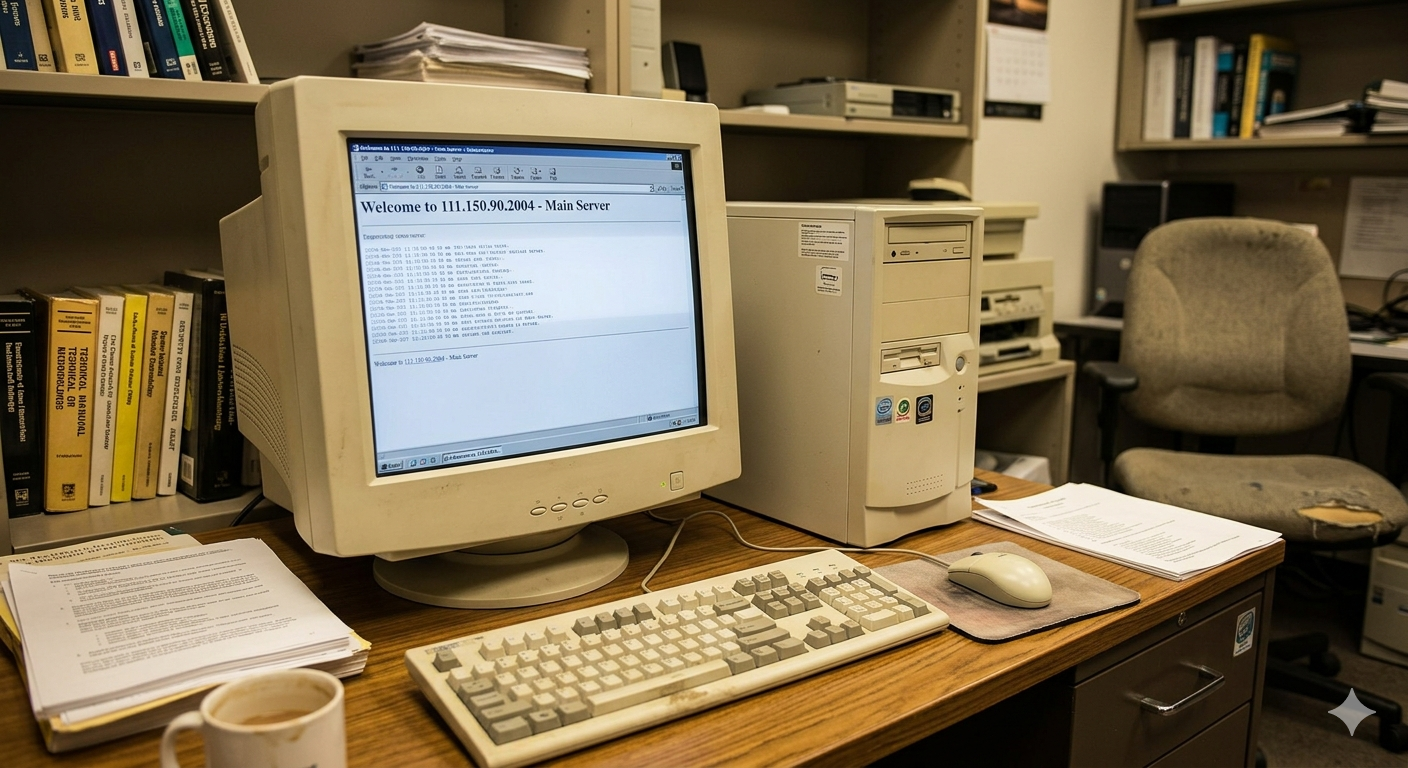
People typically encounter strings like 111.150.90.2004 in technical environments rather than everyday internet browsing. For example, it might appear in server logs when administrators are reviewing traffic patterns or troubleshooting unusual network behavior. Logs often include numeric identifiers that track connections, requests, and system events.
Another place it might appear is within software configuration files. Some enterprise systems use structured identifiers to label components such as nodes, services, or resource clusters. In those systems, dot-separated numbers can represent layered hierarchies that make it easier for administrators to organize large infrastructures.
It may also show up in analytics platforms or monitoring dashboards. Data pipelines sometimes store identifiers in dotted numeric formats to categorize events or sessions. If someone is analyzing raw log output or exported data files, they might encounter sequences like 111.150.90.2004 without immediate context, which can make them appear mysterious at first glance.
Security Considerations When Seeing Numbers Like This
Whenever unfamiliar numerical sequences appear in system logs, it’s natural to consider potential security implications. While 111.150.90.2004 itself is unlikely to represent a direct IP address, it could still be associated with system events that are worth reviewing.
For instance, some automated scanning tools generate unusual or malformed address patterns when probing networks. If a system is experiencing suspicious traffic or repeated connection attempts, administrators may see unusual numerical strings recorded in logs. In such cases, investigating the origin and pattern of those entries can help determine whether they indicate benign activity or a possible security concern.
Another important factor is log integrity. Sometimes strange number sequences appear because of parsing errors or incorrect data formatting. When logs are processed by scripts or monitoring tools, a single bug in the parsing logic can create misleading entries. Therefore, administrators should always verify whether the numbers represent real data or artifacts created by logging tools.
How to Investigate an Unknown Identifier
If you encounter 111.150.90.2004 in a technical environment, the best approach is to start by examining the context in which it appears. Look at surrounding log entries, timestamps, and related events. Often, nearby information will reveal whether the number is associated with a specific service, system component, or software module.
Another useful step is to search internal documentation or configuration files. Many systems include reference guides that explain how identifiers are structured. If the number is part of an internal naming scheme, the documentation may reveal what each segment represents. For example, the first numbers might correspond to regions or clusters, while the final number could identify a specific node or event type.
You can also review the software or service that generated the log entry. Many platforms—especially enterprise monitoring tools—use structured event IDs that resemble dotted numerical sequences. Checking the documentation for those systems often clarifies the meaning of unfamiliar identifiers.
Best Practices for Handling Numeric Identifiers in Systems
One of the most effective ways to avoid confusion with identifiers like 111.150.90.2004 is to implement clear naming conventions within technical environments. When developers and administrators follow consistent formatting rules, it becomes easier to recognize whether a number represents an IP address, version number, or internal reference.
Maintaining good documentation is equally important. Systems that rely on structured identifiers should always include clear explanations of what each segment represents. Without documentation, even experienced professionals may struggle to interpret the meaning of numeric strings found in logs or configuration files.
Finally, automated monitoring tools can help detect anomalies in log data. By analyzing patterns in system events, these tools can identify unusual entries that may indicate errors or misconfigurations. When strange identifiers appear, automated analysis can quickly highlight whether they represent legitimate system activity or something that requires further investigation.
Final Thoughts
Although 111.150.90.2004 may look like a network address, its format suggests that it is more likely an identifier, log entry reference, or misformatted numeric sequence. Understanding the context in which it appears is the key to determining its actual meaning.
In many technical environments, dotted numerical strings are used to organize complex information in a readable and structured way. While they may resemble IP addresses, they often serve completely different purposes such as tracking events, labeling resources, or identifying software versions.
If you encounter 111.150.90.2004 in your systems, the best approach is to analyze the surrounding data, review system documentation, and consider how the platform structures its identifiers. With a careful and methodical approach, even the most confusing numerical strings can be decoded and understood.